By 2026, the old way of getting leads no longer works. Paying for clicks is expensive and rarely brings in real business. Claiming you are “unhackable” only makes buyers trust you less.
Here is the bigger problem: 83% of buyers finish defining their purchase requirements before they ever contact a vendor. If you are not showing up during that research phase, you are already out of the running.
If you are a cybersecurity company thinking about outsourcing your lead generation, this guide is for you. Running a full lead generation program takes time, budget, and the right team.
Strategy #1: SEO & Authority-Led Content (The Foundation)
The cybersecurity market is noisy. Every vendor claims to be the best. To stand out, you need to pull buyers in rather than push ads at them.
When a security leader faces a new threat, they do not wait for a sales call. They search for answers online. Your goal is to be the resource they find.
LinkedIn alone accounts for 80% of all B2B leads generated through social media, according to LinkedIn’s own platform data. Being active and present on LinkedIn is no longer optional. It is a core part of keeping your pipeline full.
The “Pull” Method: Capturing Early-Phase Research
The best leads come from buyers who are actively doing research. They are looking for answers to real problems, like how to respond to a breach or how to meet a compliance deadline.
Your job is to show up with the right content at that exact moment. Target search terms tied to specific problems, such as “ransomware recovery steps” or “zero-trust implementation hurdles.” That way, your brand becomes the go-to resource when it matters most.
Core Focus: EEAT and Intent Alignment
Security buyers are trained to be skeptical. To earn their trust, you need to show real expertise. Google calls this EEAT: Expertise, Experience, Authoritativeness, and Trust.
- Answer the how-to questions: Skip the feature list. Write content that solves real problems your buyers face during the buying process.
- Publish original research: Share what you know about threat detection. Original data builds authority and sets you apart from vendors who only talk about themselves. Guest blogging on trusted industry sites is another way to build that credibility fast.
When buyers find your content helpful, they arrive at your sales call already trusting you. That makes every step of the process easier.
Strategy #2: Precision ABM with “Anti-Hype” Messaging
Buyers in 2026 are tired of “AI-powered” promises. Account-based marketing (ABM) only works if your message is specific and honest. Broad claims push buyers away. Targeted, technical messaging pulls them in.
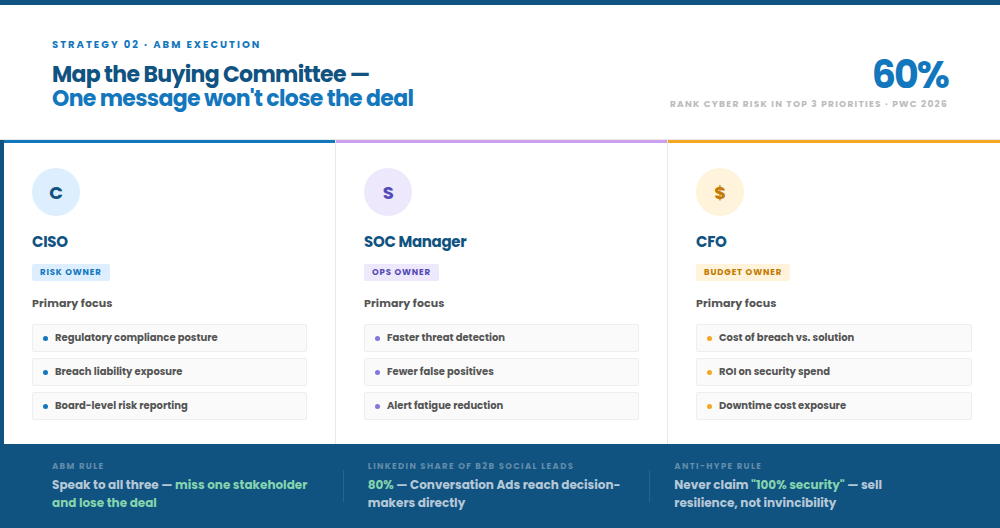
One person rarely makes the final call. Most deals involve multiple internal stakeholders and outside influencers. You need to speak to all of them. If you only talk to one contact, you risk losing the deal to someone who did not even know you existed.
The “Anti-Hype” Rule: Selling Resilience
Smart buyers know that “100% security” is not real. Do not claim it. Instead, focus on what you can actually deliver: faster response times, less downtime, and better visibility into threats.
This kind of honesty is rare. It sets you apart from firms that over-promise and under-deliver.
Mapping the Buying Committee
Each person on the buying team cares about something different. Your content needs to speak to each of them across the full sales cycle:
- The CISO: Cares about risk, compliance, and what happens if something goes wrong.
- The SOC Manager: Wants faster threat detection and fewer false alarms.
- The CFO: Needs to know the cost of a breach versus the cost of your solution.
According to PwC’s 2026 Global Digital Trust Insights survey, 60% of business and technology leaders now rank cyber risk investment among their top three strategic priorities, driven by geopolitical uncertainty. Your marketing should speak to that level of urgency.
Tactical Execution: LinkedIn Conversation Ads
LinkedIn Conversation Ads let you reach decision-makers directly. They feel less like an ad and more like a peer-to-peer message. For a broader look at turning social channels into a lead engine, see our guide on social media lead generation.
Offer something useful, like a whitepaper or a case study. Do not go for the hard sell right away. This builds trust and brings higher-quality leads into your pipeline.
Strategy #3: Value-Based Outbound & Appointment Setting
SEO and ABM bring buyers to you. But you also need to go out and find them. In 2026, outbound is not about sending mass emails. It is about reaching the right person at the right time with the right message.
Speed-to-Lead as a Competitive Differentiator
When a lead downloads a checklist or reads a guide, follow up fast. Your sales team should reach out within minutes, not days. The goal is not to sell on that first call. It is to offer more help and start building trust. The first firm to show up with real value usually wins.
TAM Analysis: Radical Market Focus
You cannot close deals with companies that are not a fit. Before you run any outbound campaign, define your target market clearly. Use research and data tools to build a list of firms with the right budget and tech stack. Every contact in your outreach should be a real potential buyer.
Appointment Setting: Redefining the KPI
The goal is not more leads. The goal is more meetings. Learn how the full B2B appointment setting process works and what it takes to build a pipeline of qualified calls.
Metric | Traditional Approach | 2026 Strategy |
Primary KPI | Number of Clicks/Downloads | Scheduled Discovery Calls |
Sales Focus | Generic Cold Calling | Value-Based Outreach |
Outcome | Clogged Sales Funnel | High Pipeline Velocity |
When you focus on booked meetings instead of raw leads, your sales team spends time on buyers who are ready to talk. That leads to faster deals and less wasted effort.
Strategy #4: Interactive Data Capture (The “Proof” Strategy)
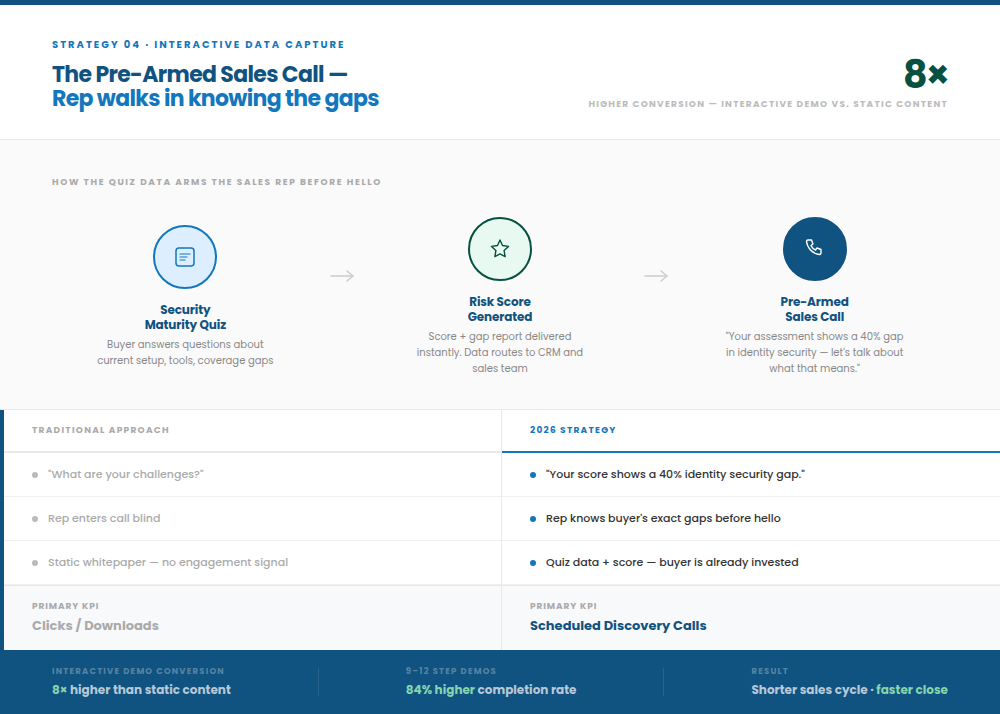
Static whitepapers no longer move buyers. In 2026, you need to show buyers what their gaps look like, not just tell them. Use the prospect’s own data to make the case.
Buyers who engage with an interactive demo convert at nearly 8 times the rate of those who do not, according to Storylane data. And demos built around 9 to 12 steps see an 84% higher completion rate than shorter ones, based on Arcade’s analysis of 14 million sessions.
Self-Assessment Tools: Quantifying Risk
A security maturity quiz or risk scorecard is one of the most powerful lead tools you can use. Pairing these tools with an optimized landing page makes sure none of that traffic goes to waste. Buyers answer questions about their current setup. You give them a score and a clear picture of their gaps.
For you, the quiz does two things. It gives buyers real value right away. And it tells your sales team exactly where each lead stands before the first call.
Survey-Led Lead Gen: The Power of Proprietary Data
Collect data from your audience and turn it into a report. A regional threat report, for example, is something security leaders want to read. It shows you know the market. And it brings in buyers who want to benchmark themselves against their peers.
For help collecting this data, see our guide on optimizing contact forms for lead generation.
The “Pre-Armed” Sales Call
When a lead fills out your quiz, that data goes straight to your sales team. Your rep does not walk into the call blind. They already know the buyer’s gaps.
Instead of asking “What are your challenges?”, your rep can say: “Your assessment shows a 40% gap in identity security. Let’s talk about what that means for your business.” That kind of opening builds trust fast and shortens the sales cycle.
Strategy #5: Behavioral Lead Scoring & Intent Data
In cybersecurity, timing matters as much as the message. You do not want your sales team chasing cold leads. You want them to reach out when a buyer is ready. Lead scoring helps you do that automatically.
Intent Data Tracking: Monitoring the “Invisible” Journey
Intent data lets you see what companies are researching online, even before they fill out a form. You can track which firms are looking up specific CVEs (Common Vulnerabilities and Exposures) or comparing your solution to a competitor’s, before they ever raise their hand.
This gives you a head start. You can reach out while the buyer is still in research mode, before they have a shortlist.
Behavioral Thresholds: The “Sales Ready” Trigger
Not every click means a buyer is ready. Set clear rules for when to act. For example:
- Trigger: A lead visits your pricing page and downloads a post-breach case study.
- Action: Your sales team gets an alert and reaches out right away.
This way, your team only contacts leads who have shown real buying intent. No more chasing every click.
Omnichannel Nurture: Constant Technical Presence
If a lead goes quiet, do not give up. Send a follow-up email. Then run a LinkedIn ad with a relevant success story. Each touch keeps you visible and builds your credibility. Consistent, helpful outreach moves leads toward a conversation over time.
How LeadAdvisors Runs This Infrastructure for Cybersecurity Companies
These five strategies are not a simple checklist. Each one takes real work: content production, outbound campaigns, appointment setting, lead qualification, and ongoing improvement. Most cybersecurity companies do not have the time or resources to build all of this in-house.
LeadAdvisors builds and runs this infrastructure for cybersecurity clients. Your team focuses on closing deals and delivering results. If you want to understand the full lead generation picture before we talk, start with our complete guide on how to generate B2B leads.
What LeadAdvisors manages:
- Authority content and SEO: We write the technical content that gets your firm found during the research phase. This is the same work covered in our Cybersecurity SEO guide: we do not just explain it, we do it for you.
- Outbound contact campaigns: We build targeted outbound sequences for your ideal buyer. Every campaign starts with TAM analysis and data research so you reach real prospects, not random contacts.
- Appointment setting: Our SDR team works as part of your sales function. We turn high-intent leads into booked discovery calls. You pay for meetings, not just names on a list.
- Lead qualification and scoring: We set up the scoring rules and intent tracking so your sales team only gets leads that are ready to talk, not a pile of contacts to sort through.
- QA infrastructure: Every campaign, content piece, and lead handoff goes through a review process. By the time a lead reaches your team, they have already been checked against your criteria.
The result is a program that runs every day, without you needing to hire a full team or spend months building it from scratch.
The best place to start is a strategy session. We look at your current setup, find the gaps, and show you what a managed program would look like for your firm.
Book a strategy session with LeadAdvisors →
Frequently Asked Questions
Why should cybersecurity firms prioritize "Cost Per Meeting" (CPM) over "Cost Per Click" (CPC)?
How do we engage highly skeptical technical buyers during the initial outbound phase?
What role does "Intent Data" play in shortening complex sales cycles?
Can small cybersecurity companies compete with industry giants in SEO?
Is cold calling still effective for generating cybersecurity leads in 2026?
Conclusion: Building a Lead Generation Engine
One tactic on its own will not get you far. You need a full system where content builds trust, ABM targets the right people, and outbound turns intent into booked meetings.
When you shift focus from vanity metrics to real buying signals and cost per meeting, lead generation stops being a cost and starts being a growth engine. These five strategies are the full model. LeadAdvisors runs all five for cybersecurity companies that want to close more deals without building the infrastructure themselves.