Let’s face it: in the security space, trust is the only currency that really matters. But even if a solution is impenetrable, it won’t grow if the potential customers can’t find it. That is why cybersecurity SEO should be a mandatory part of your business expansion; essentially, it involves securing a search engine optimization plan that demonstrates your expertise even before a lead clicks on “Book a Demo.”
This exclusive framework merges technical SEO for cybersecurity (site hardening) with a top-notch content strategy. If you optimize for the right keywords and have good E-E-A-T (Experience, Expertise, Authoritativeness, and Trustworthiness), you can attract CISOs and IT directors, which essentially translates into a lead generation engine with a high ROI.
Quick Audit Checklist
- Security: Is your website running on HTTPS with a valid Content Security Policy (CSP)?
- Authority: Are the experts’ bios with the credentials they have been verified by linked to each technical blog post?
- Content: In your guides, do you give a clear definition of “What is [Threat]? ” within the first 100 words?
What Is Cybersecurity SEO?

Cybersecurity SEO is the strategic process of positioning your brand as the definitive authority on digital protection. In an industry built on risk mitigation, SEO is about more than just ranking for keywords; it is about engineering trust before a single conversation ever takes place.
When you optimize for cybersecurity, you aren’t just selling software—you are selling peace of mind. Your strategy must achieve three core objectives: reaching high-level decision-makers, generating high-intent leads, and establishing an unbreakable reputation.
The Unique Challenges of the Security Sector
Unlike retail or lifestyle SEO, cybersecurity requires a high-stakes B2B approach. As industry experts like Yoav Bernstein note, the barriers to entry are significantly higher due to several critical factors:
Bridging the “Tech-Speak” Gap: Your content must be dual-purpose. It needs to satisfy the technical scrutiny of IT managers while clearly communicating ROI and business resilience to the C-suite.
Compliance & “Practice What You Preach”: If a security firm’s website lacks basic HTTPS encryption or displays technical errors, credibility vanishes instantly. A security company with a vulnerable site is like a locksmith with a broken front door.
Defending Against SEO Poisoning: In this niche, you must actively protect your rankings. Malicious actors often attempt “Google poisoning” to hijack high-ranking security terms to spread malware, making your own site’s defense part of your SEO strategy.
The Bottom Line
Whether you are a startup focused on SaaS growth or an established firm undergoing a technical audit, the goal remains the same: to be the most visible, most trusted authority in the search results. Success requires a blend of technical precision, emotional resonance with the buyer’s pain points, and a relentless commitment to digital hygiene.
The Synergy Between SEO and Cybersecurity
Here’s something most people overlook: SEO and actual site security are two sides of the same coin. They don’t just “work together”—they are codependent. If you ignore one, the other eventually collapses.
When Cybersecurity Fails, SEO Suffers
Search engines are in the business of trust. If your site is hit by an SEO attack or malicious actors use SEO hacking to turn your blog into a host for malware, Google will drop your rankings faster than a zero-day exploit.
Hacked or slow-loading sites get flagged immediately. Even “small” lapses—like a missing SSL certificate or failing to follow secure vs. non-secure site ranking best practices—will cost you significant organic traffic. If a user sees a “Connection Not Private” warning on a security firm’s site, they aren’t just leaving—they are never coming back.
When SEO is Weak, Credibility Suffers
In this industry, your digital footprint is your resume. If a CISO searches for a specialized agency and finds a site with broken links, poor formatting, or outdated content, they’ll assume your software is just as neglected.
If you aren’t visible, you don’t exist; but if you’re visible and look unprofessional, you’re a liability. As Yoav Bernstein emphasizes, reputation management is the core of any high-level cybersecurity SEO strategy.
The Power of the “Secured Search” Strategy
Combining your technical SEO with actual hardening protocols results in a strong “Secured Search” flywheel:
- Higher Search Rankings: Google favors fast, secure, and trustworthy sites with high search rankings.
- Immunity to SEO Poisoning: With a tighter optimization strategy, you are one step ahead of those who would attempt to manipulate search engines and perform search engine poisoning.
- Greater Customer Confidence: High search rankings combined with a secure padlock icon translate to an instant “trust signal.”
To avoid the risk of being blacklisted by Google and harming your brand for years, you must ensure that these two components work perfectly together. Whether you are growing a global SaaS or concentrating on local services, your SEO endeavors need to be as secure as your data.
Core Cybersecurity SEO Strategies
Start by watching real searches, not hunches. A clear method spots valuable terms without risking how others see your name.
A. Keyword Research & Content Strategy
Picture this: every search has a reason behind it. Without knowing the reason, guesses replace strategy. Think of aiming without seeing the target. Clarity begins when purpose drives decisions. What matters shows up only after asking why.
I recommend starting with “boots-on-the-ground” research:
- Google Autosuggest: For a look at real-time trending searches.
- People Also Ask: For discovering the very specific questions your audience loses sleep over.
Once you’ve gathered the basics, level up with industry-standard tools like Ahrefs, Semrush, or SEO Watcher. These help you identify:
- Competitor Gaps: Terms your rivals rank for that you’ve missed.
- Long-Tail Queries: Specific phrases like “cybersecurity audit for small business” or “managed detection and response pricing.”
- Niche Identifiers: Specific expert-led terms or geographic markers like “Gold Coast cybersecurity services.”
Mapping the Buyer’s Journey
A CISO wants technical depth, while a CEO wants to hear about risk mitigation and ROI. You must tailor your content to match their specific stage in the funnel:
Funnel Stage | Search Intent Example | Content Type |
Top (Awareness) | “What is SEO poisoning?” | Educational Blog |
Mid (Consideration) | “Best B2B security services” | Comparison Guide |
Bottom (Decision) | “Cybersecurity agency near me” | Service Page / Case Study |
B. High-Quality, Expert-Led Content

In the world of SaaS SEO, thin content is a death sentence. You have to prove that you’re the smartest person in the room without being the most boring.
Here is how you establish authority:
- Double Down on E-E-A-T: Google cares about Experience, Expertise, Authoritativeness, and Trustworthiness. So should you. Expert bios, whitepapers, and other sources like NIST and CISA.
- Combat Misinformation: Help your readers avoid pitfalls. A post about SEO poisoning, for example, helps your readers avoid it and establishes you as the hero.
- Prioritize Clarity: Even the most technical of readers will appreciate your use of bullet points, bolding, and easily readable H2 and H3 headings.
- Leverage Social Proof: There is nothing more effective than a cybersecurity SEO case study. Show your readers how your SEO strategy helped increase demo requests by 50% or protect your client’s reputation.
By aligning your strategy with your audience’s needs, you don’t just get traffic, you create a sales funnel of people who trust your brand.
Technical SEO for Cybersecurity Sites
Let’s talk about the engine under the hood. Technical SEO is not just about making things work; it’s about making your site a fortress that Google trusts. If your site is slow or appears vulnerable, you’re not just losing rankings; you’re losing your reputation.
A. Website Security & SEO
In this industry, security is the ultimate ranking signal. So, if the visitor detects the “Not Secure” label, they will leave the site as quickly as they would if they were not able to log in. To have the Google-secured label, you need to look beyond the SSL certificate.
My recommendation is:
- Web Application Firewalls (WAF): This blocks malicious bots before they can launch an SEO attack.
- Content Security Policy (CSP): This stops XSS attacks and malicious script injections, which lead to search engine optimization poisoning.
- HSTS (HTTP Strict Transport Security): This enforces secure connections so you can stay ahead of Google’s secure vs. non-secure ranking benchmarks.
- Regular Malware Scans: This ensures your site is not being used for search engine phishing or Google poisoning.
B. Site Performance
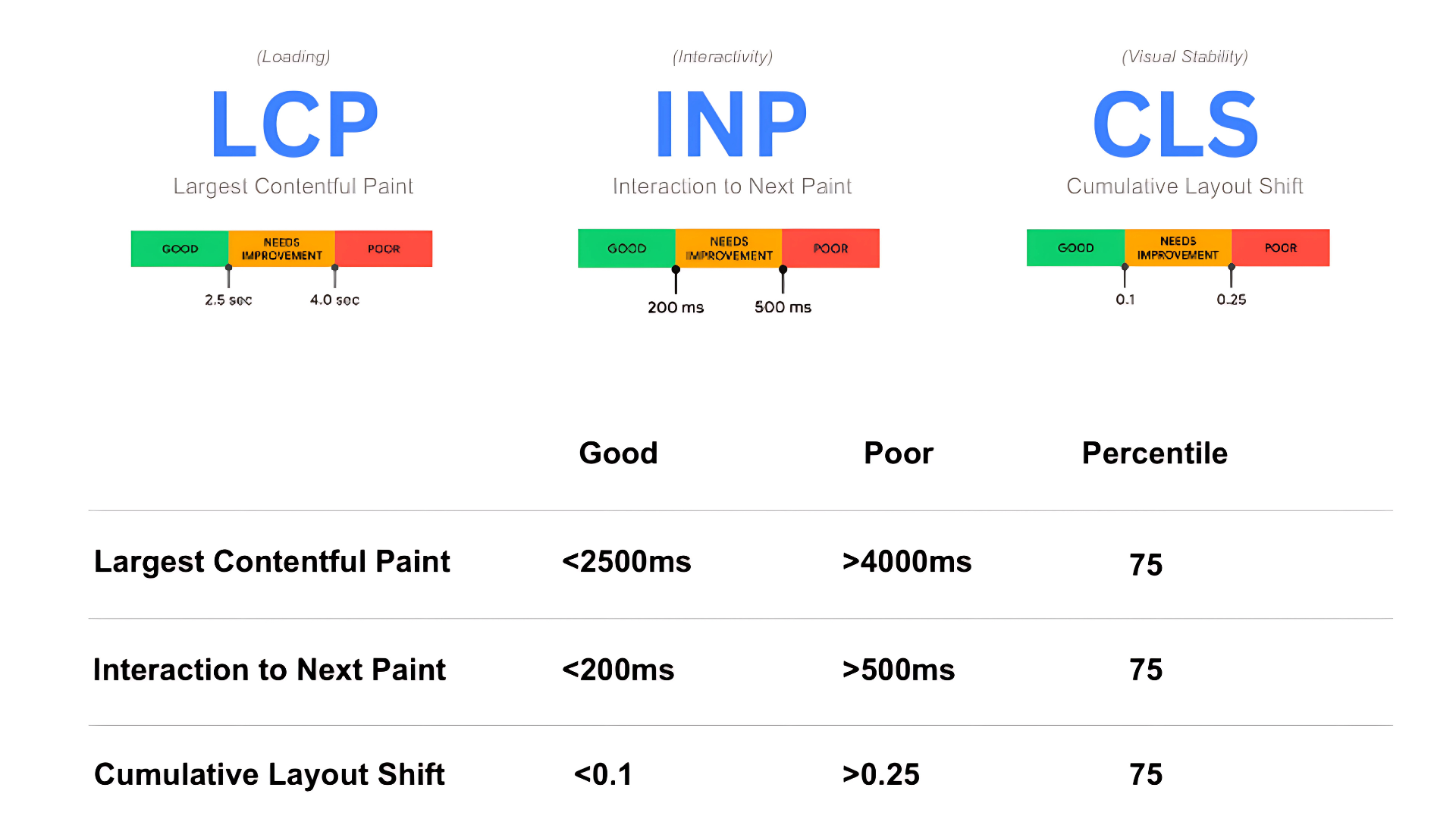
Speed is another security feature. If your website is slow, it means your backend is bloated and unoptimized, which isn’t the kind of image a security leader wants to project. Your main scorecard for optimization comes from Google’s Core Web Vitals:
- LCP (Largest Contentful Paint): This measures the speed at which your main content is loading.
- INP (Interaction to Next Paint): This measures the speed at which your website responds after a click.
- CLS (Cumulative Layout Shift): This ensures that your content isn’t jumping around the page, which could be interpreted as a “poison search” redirect.
Optimize by using clean code, compressed images, and SEO watcher tools to monitor for performance spikes or anomalies.
C. Crawlability & Indexation
You must be able to handle search engine crawlers like a pro. So, when Googlebot is unable to find your valuable threat reports, they might as well not exist.
- XML Sitemaps & Robots.txt: Help the good bots target your keywords and avoid your sensitive areas.
- Schema Markup: Help Google understand your content with Organization, Service, and FAQ schema.
- Canonical Tags: Avoid duplication problems that often plague you when your website is crawled across multiple sub-domains or staging versions.
By mastering these basic website building blocks, you ensure your website is just as robust as your offerings. The difference between a “hobbyist” blog and a real professional online presence with high authority.
Local SEO for Regional Cybersecurity Firms
The thing is, you could have the most advanced SOC in the nation, but if a local business owner is looking for a “cybersecurity firm near me” and they can’t find you, they’re essentially throwing money out the window.
Local SEO is an extremely targeted strategy that allows your customers to find and trust you before they find your competitors. You could be providing Gold Coast cybersecurity services, or managing SEO for Mount Tamborine, and local SEO is your secret weapon.
Problem #1: No Google Business Profile
The Fix: Claim and optimize your GBP immediately. Treat this as your digital storefront. Fill out every section: services, specific categories (like “Computer Security Service”), hours, and high-quality images of your team in action. This is the fastest way to break into the “Local Pack.”
Problem #2: Inconsistent Business Info
The Fix: Keep your Name, Address, and Phone (NAP) perfectly consistent across the web. If your office is “Suite 200” on your site but “Ste 200” on Yelp or Clutch, search engines get confused. Consistency builds trust with Google and clients alike.
Problem #3: No Location Targeting on Website
The Fix: Don’t just try to rank for “cybersecurity.” Create dedicated local landing pages. Use specific terms like “Penetration testing in [City Name]” or “Compliance audits for [Region] businesses.” This signals your relevance to specific geographic markets.
Problem #4: No Local Content
The Fix: Produce content that matters to your neighbors. Write about regional compliance laws, local industry risks, or your involvement in community tech events. This increases relevance and draws in high-intent, regional organic traffic.
Problem #5: Few or No Reviews
The Fix: Actively encourage satisfied clients to leave reviews on Google, G2, or Clutch. In a world of SEO manipulation, authentic local feedback is the ultimate trust signal.
Pro-Tip: If you’re a B2B firm focusing on regional growth, combine your local landing pages with local link-building. A backlink from a local Chamber of Commerce or a regional tech hub is worth its weight in gold for your domain authority.
Link-Building & Digital Authority

In the world of cybersecurity, a backlink isn’t just a “vote” for your website—it’s a digital voucher for your trustworthiness. You aren’t just competing for a spot on page one; you’re persuading cautious, security-minded buyers that you won’t let them down.
That’s why a high-level authority strategy isn’t about shortcuts. If you use unethical SEO or “dark” tactics like link farms, you aren’t just risking a Google penalty—you’re signaling to your clients that you take shortcuts with security, too.
Pillar 1: Build Authority Through Thought Leadership
Authority begins with unique insight. When your team has unique threat intel or unique commentary on emerging trends, you’ll achieve the coveted “Natural Links” that Google loves.
- Contribute Guest Posts: You want to target tech stacks or security-focused sites.
- Get Quoted: You want to position your leadership as thought leaders who can provide quotes for large reports.
- Tier-1 Collaborations: Being mentioned within Wired, CSO Online, or Infosecurity Magazine is a massive win. This is not a link; this is a “Trust Signal” that says your opinions are important.
Pillar 2: Expand Reach With Editorial Reviews
In the SaaS SEO world, third-party validation is king. High-authority editorial reviews—expert-written pieces living on external sites—are designed to rank for “Best of” queries and persuade hesitant buyers. These reviews:
- Showcase your product features using industry best practices.
- Strengthen your branded presence (dominating more “real estate” on page one).
- Improve E-E-A-T signals by showing that independent experts vouch for your solution.
Pillar 3: Play the Long Game
There is a massive difference between genuine optimization and SEO manipulation. Firms that try to “game the system” with paid link schemes or search engine optimization poisoning tactics always end up losing.
Stay away from:
- Paid Listings & Link Farms: These are easily detected and can lead to being blacklisted.
- Doorway Pages: These create a poor user experience and trigger red flags for search engine crawlers.
- SEO Hacking: Never use unethical tactics to gain an edge. It is the fastest way to destroy a cybersecurity brand’s reputation.
Instead, focus on earned links and scalable editorial partnerships. Whether you are an in-house team or working with a specialized agency, remember: Authority is built on intention, honesty, and quality—the same principles your security solutions are built on.
Cybersecurity Press Releases for SEO
Think press releases are just for old-school PR firms? Think again. In the modern landscape, a well-timed press release is a strategic power move. It is one of the fastest ways to build “News” authority, earn high-quality backlinks, and signal to Google that your brand is an active, trusted player in the security space.
When to Pull the Trigger
To move the needle on your organic visibility, only publish when you have genuine “trust-building” milestones. Avoid spamming the wire with fluff; instead, focus on:
- Product Launches: Bringing a new AI-powered threat detection tool to market?
- Compliance Wins: Passing a SOC2 Type II or FedRAMP audit is a massive E-E-A-T signal.
- Threat Intelligence Reports: Publishing original research on a new SEO poisoning trend makes you a primary source for journalists.
- Strategic Partnerships: Teaming up with a major cloud provider is gold for digital authority.
How to Optimize for the “Search Bots”
To maximize ROI, treat your press release like a high-performance landing page:
- Keyword-Rich Headlines: Instead of “Company X Announces New Feature,” use specific terms like “Company X Launches Zero-Trust Architecture to Combat Search Engine Poisoning.”
- The Inverted Pyramid: Put the “Who, What, Where, and Why” in the first paragraph. This assists AI-adaptive SEO, as crawlers look for quick, factual summaries.
- Schema Markup: Implement NewsArticle or PressRelease schema so Google News can categorize you correctly.
- Multimedia Optimization: Include relevant images with descriptive alt tags (e.g., “Dashboard view of threat detection”) to rank in Image Search.
Distribution: Quality Over Quantity
Don’t throw your release into a generic “link farm”—that borders on unethical SEO and won’t help your rankings.
- Self-Publish First: Post it on your own “Newsroom” or blog to ensure you own the primary version.
- Syndicate to Niche Outlets: Use services like CyberNewswire or industry-specific hubs. This provides high-quality backlinks from relevant domains.
- Social Amplification: Share it on LinkedIn to catch the eye of industry experts and potential B2B buyers.
The Long Game of Brand Authority
Each release is a brick in your “Wall of Trust.” Over time, a steady stream of optimized releases builds a Knowledge Graph around your brand. This tells search engines you are a living, breathing entity that is constantly innovating—the kind of consistent visibility that eventually displaces competitors who are still playing “catch-up.”
Measuring SEO Success in Cybersecurity
If you aren’t tracking your data, you’re essentially flying blind in a storm. In this space, success isn’t just about a spike in “vanity metrics” like raw traffic; it’s about high-intent visibility and proving your digital authority.
Think of your SEO data as your “Marketing SOC.” You need to monitor it constantly to see what’s working, what’s under attack, and where your strategy needs a “patch.”
The “Security-First” SEO Dashboard
To truly understand your ROI, use the right industry tools (like Ahrefs, Semrush, and Google Search Console) to track these specific KPIs:
Metric | What It Actually Tells You | Pro Tools |
Organic Traffic | Are your target keywords bringing in the right humans? | GA4, GSC |
Keyword Rankings | Your progress on competitive terms like “Managed EDR.” | Semrush, SEO Watcher |
Engagement Rate | Are visitors actually reading your threat reports? | Google Analytics 4 |
Leads & Conversions | The “Bottom Line”—did that blog turn into a demo? | GA4, ConversionIQ |
Backlink Profile | The health of your authority and industry mentions. | Ahrefs, Majestic |
Indexing Status | Are your pages visible or blocked by technical errors? | Google Search Console |
Why These Metrics Matter
Consistently tracking these KPIs shows the real-world impact of your SEO activity. In a sector where trust is the ultimate currency, even a small gain in rankings for a high-intent term like “B2B security services” can lead to massive enterprise contracts.
Furthermore, monitoring your data helps you spot anomalies. A sudden, unexplained drop in rankings or a spike in “weird,” low-quality traffic could be a sign of SEO manipulation or a search engine poisoning attempt against your brand.
Acting on the Insights
Don’t just look at the numbers—use them to pivot.
- If Engagement is low for a technical guide, simplify the language or improve the layout.
- If a case study is getting high traffic but zero clicks, move your “Book a Demo” button higher.
This is how a B2B cybersecurity company stays agile, protects its reputation, and dominates the SERPs.
Common Pitfalls & Cybersecurity SEO Mistakes
Even with the best intentions, it’s easy to trip over invisible wires that tank your rankings. In 2026, Google’s algorithms are smarter, and users are less patient. If you want to stay visible, you have to avoid these five classic “self-pwns.”
1. Ignoring Website Security
Skipping HTTPS, falling behind on SSL renewals, or neglecting malware protection is a total dealbreaker. Search engines prioritize user safety; if your site is flagged as “Not Secure,” you’ll face deindexing, blacklisting, and a massive rank loss. For a security firm, this isn’t just an SEO mistake—it’s a catastrophic blow to your brand’s core promise.
2. Writing Only for Technical Audiences
It’s tempting to fill your pages with deep technical specs, but remember: the person signing the check is often a CEO or CFO, not just a SysAdmin.
- The Pitfall: Overloading content with “alphabet soup” (MDR, XDR, SIEM, SOAR) without context.
- The Fix: Create a “dual-track” content strategy. Use high-level value propositions for executives and technical deep-dives (whitepapers or documentation) for the IT team. If they can’t understand your value, they won’t convert.
3. Treating SEO as a One-and-Done Project
SEO isn’t a one-time patch; it’s an ongoing operation. I’ve seen firms hit page one, stop their SEO activity, and disappear from search results three months later.
- The Danger: Content decay and aggressive competitor movement.
- The Fix: Treat your organic strategy like your threat intelligence feed. Perform regular keyword updates, audit your backlink profile for unethical SEO spam, and keep a constant eye on Google Search Console for new crawl errors.
4. Neglecting Mobile Experience
With mobile devices driving over 60% of B2B research in 2026, a clunky mobile layout is a ranking killer.
- The Mistake: Having buttons that are too small to tap or complex technical charts that don’t scale on a smartphone.
- The Impact: Google’s mobile-first indexing will penalize your desktop rankings if your mobile site is frustrating to use.
5. Not Using PR for Social Proof
Many firms think Press Releases are just for the news cycle. In reality, they are essential for digital authority.
- The Gaps: Failing to optimize releases with target keywords or neglecting to link back to core service pages.
- The Fix: Use well-crafted PR to announce new audits, partnerships, or threat research. It builds the “Social Proof” that both users and Google’s AI Overviews crave.
Avoiding these pitfalls doesn’t just preserve your rankings—it builds a user-friendly brand that people actually trust.
Future Trends: AI, Zero-Click, and SEO for Cybersecurity
Cybersecurity SEO is evolving faster than a zero-day exploit. Staying ahead means preparing for what’s next, not just optimizing for what worked yesterday. As we move through 2026, the fusion of AI and cloud security trends is fundamentally shifting how CISOs and IT directors find solutions.
AI Overviews & Zero-Click Search
Google’s AI Overviews (AIO) and featured snippets now allow users to get complex security answers without ever leaving the search results page. In fact, recent data shows that organic CTR can drop by over 60% when an AI summary is present.
To win in this “zero-click” world, you need to stop just “ranking” and start becoming the source the AI cites. When your brand is cited in an AI Overview, your organic clicks can actually jump by 35%. To get there, your content must be:
- Highly Structured: Use clear H2/H3 headers and bullet points.
- Definition-Focused: Provide concise “What is [X]?” answers at the top of your technical guides.
- Data-Backed: AI-adaptive strategies prioritize content with original threat intel, proprietary stats, and expert citations.
The Rise of Programmatic SEO
Programmatic SEO is becoming the gold standard for scaling long-tail reach. By using data templates, you can automatically generate hundreds of high-quality pages for specific queries like “Best firewall for [Industry]” or “Compliance requirements for [State].”
Firms using pSEO for “Integration” and “Compliance” pages have seen traffic growth exceeding 200%. This approach captures niche, high-intent searches that competitors often ignore.
AI + SEO + Cybersecurity: A Strategic Trio
AI isn’t just changing how people search; it’s changing how you protect your rankings. With the rise of SEO poisoning, the future of organic growth is defensive.
- Autonomous Content: Use AI to convert live threat intel into real-time blog updates.
- Predictive SEO: Anticipate shifts in search interest before a major breach hits the news.
- E-E-A-T is Non-Negotiable: Because anyone can use AI to write a blog, Google is doubling down on Experience, Expertise, Authoritativeness, and Trustworthiness. Only human-led, expert-verified content will survive the “AI noise.”
The future of cybersecurity SEO is a fusion of agile AI tools and deep human authority. It’s about reaching users with the right answer before they even finish typing their query.
Partner or DIY? When to Hire a Cybersecurity SEO Expert
Let’s be honest: running a security firm is a 24/7 job. Between mitigating ransomware and patching vulnerabilities, finding the time to master search engine optimization can feel like trying to solve a Rubik’s Cube in the dark.
The question is: should you handle your SEO activity in-house, or is it time to bring in the pros?
The DIY Route
If you have a nimble marketing team and access to industry tools like Semrush, Surfer, or Screaming Frog, you can start the journey yourself.
- The Benefit: Total control over the technical nuances and messaging of your product.
- The Risk: Without a specialized SEO strategy for cybersecurity, it’s easy to focus on vanity keywords or miss critical technical requirements like CSP headers and schema markup.
The Specialist Route: Hiring a Cybersecurity SEO Agency
For most firms, the fastest path to page one is partnering with a specialized B2B cybersecurity SEO agency. This isn’t just about “outsourcing”—it’s about hiring a team that speaks your language.
When vetting an agency or an expert like Yoav Bernstein, look for these non-negotiables:
- Industry Intel: Do they know the difference between EDR and XDR? An agency that doesn’t understand your tech will write jargon-heavy fluff that fails to convert CISOs.
- Ethical Foundations: In this sector, reputation is everything. Ensure they avoid unethical SEO or “dark” tactics. You need “White Hat” strategies that protect your brand from search engine poisoning and SEO hacking.
- Proven Data: A top-tier partner should provide a cybersecurity SEO case study showing how they moved a client from page 10 to the “Local Pack” or top organic spots.
- Authority Building: Look for connections with platforms like CyberNewswire. Building digital authority requires high-level PR and editorial reviews, not just blog posts.
The Hybrid Option: SEO for Resellers
Some firms choose a middle ground by using white-label SEO services. This allows you to offer expert support to your own clients (like MSPs or resellers) without building an entire department from scratch. It’s an efficient way to scale while staying focused on your core security products.
Whether you go DIY or hire a specialist, remember: cybersecurity SEO isn’t a “one-and-done” project. It’s a long-term investment in your brand’s visibility, trust, and sustainable growth.
Frequently Asked Questions
How long does it take to see results from cybersecurity SEO?
Can SEO help us recover from a cybersecurity incident or breach?
Should cybersecurity companies invest in paid ads or focus only on SEO?
What’s the difference between SEO for SaaS cybersecurity tools and managed service providers (MSPs)?
How can we create cybersecurity content that’s both technical and accessible?
Final Thoughts: SEO as a Growth Lever for Cybersecurity
At the end of the day, cybersecurity SEO is about more than rankings—it’s your digital reputation. Before a client ever speaks to you, they judge your trustworthiness by your search visibility and the authority of your content.
SEO is a reputation engine that compounds in value when built on expertise and ethical practices. While shortcuts like unethical SEO eventually fail, a foundation of visibility and trust drives sustainable, long-term growth for your cybersecurity company.